In our second and final part of Pesh Framjee's article on fraud prevention, Pesh explores lines of defence and appropriate controls, and shares a number of helpful fraud case studies.

Internal controls
ISA (UK and Ireland) 315 explains that internal control is the process designed and effected by those charged with governance and management and other personnel to provide reasonable assurance about the achievement of the entity’s objectives with regard to reliability of financial reporting, effectiveness and efficiency of operations and compliance with applicable laws and regulations.
It follows that internal control is designed and implemented to address identified business risks that threaten the achievement of any of these objectives. It is a responsibility for management to decide the extent of the internal control systems appropriate to the enterprise.
For charities, there will always be a cost versus benefit trade-off, as well as the problem that it is often difficult to impose onerous controls on all areas. No internal control system can by itself guarantee efficient administration and completeness and accuracy of the records.
Large non-profits should have the internal controls appropriate to any large enterprise and the auditor should look for and encourage the organisation to implement internal controls and reporting systems in keeping with the scale of operations. Controls should be both financial and operational.
The organisation should have a procedure for identifying and responding to fraud. Lessons to be learnt need to be considered and whenever there is an incident of fraud. The thinking should be:
- What allowed this to happen?
- What is the extent of the risk?
- Could it still be happening elsewhere in the organisation?
- How was it detected?
- What procedures need to be implemented to prevent the risk of recurrence?
Matters to consider
- Does the organisation have a fraud register?
- Does the organisation have a fraud response plan?
- Are there whistle blowing guidelines?
The Board and, through them, senior management, are responsible for establishing and maintaining adequate accounting and other records and internal control systems.
In fulfilling that responsibility they must assess the expected benefits and related costs of management information and of control procedures.
The objective is to provide reasonable, but not absolute, assurance that assets are safeguarded against loss from unauthorised use or disposition, that operations are properly monitored and evaluated, that transactions are executed in accordance with established procedures and are recorded properly, and to enable the organisation to conduct operations in a prudent manner.
Because of inherent limitations in any accounting and internal control system, errors or irregularities may nevertheless occur and not be detected.
Also, projection of any evaluation of the systems to future periods is subject to the risk that management information and control procedures may become inadequate because of changes in conditions or that the degree of compliance with those procedures may deteriorate.
Decentralised operations
There is often more to the organisation than the head office location. Many non-profits have decentralised operations.
Empowerment is a popular concept in the non-profit sector and often much control is devolved to individuals who are trusted to do the right thing.
It is important to ensure that there are adequate controls to detect if things are going wrong. This means that there is a need to understand and document the operating environment.
How many locations are there (branches, regional offices, project offices etc)? What is covered by external audit cover? What is covered by internal audit or other auditors? What satisfaction can be gained by relying on the work of others?
The fraud risk can be exacerbated when non-profits operate internationally and in challenging environments. The reasons for this are many. Sometimes, controls in remote locations are weaker, the business ethic may be different, socio-economic factors may make whistleblowing less effective.
Assurance framework and the three lines of defence
Many non-profits make a significant investment in ‘assurance’. In addition to external and internal audit, there are other ‘hidden’ assurance costs and it is important that all this is coordinated to ensure maximum benefit.
This entails understanding the level of assurance we see with most charities – in effect clarifying who does what, where, and when. There are many tasks, services and activities that typically provide assurance in the non-profit framework.
These include:
- the oversight of the board and sub committees
- external audit
- internal audit
- external audit at overseas offices
- other review and extended assurance work
- reviews by the staff (capacity building and review visits)
- audits by and for funders (on an ad-hoc basis).
In my experience, most non-profits have historically not been very good at understanding the different levels of assurance and properly identifying how all these should be coordinated to provide a joined up assurance framework.
Assurance for a non-profit has diverse aspects. In addition to the traditional areas of financial control, there is a need to factor in the specific issues that arise from the operating structure and local environment.
A key question is: ‘what assurance does the organisation have that key controls to manage risk are in place and operating efficiently and effectively?’
This will require the building of an assurance framework and assurance maps. Assurance mapping is a mechanism for linking assurances from various sources to the risks that threaten the achievement of the organisation’s outcomes and objectives. They can be at various levels, dependent upon the scope of the mapping.
Three lines of defence
A concept for helping to identify and understand the different contributions the various sources can provide is the Three Lines of Defence model.
By defining the sources of assurance in three broad categories, it helps to understand how each contributes to the overall level of assurance provided and how best they can be integrated and mutually supportive.
For example, management assurances could be harnessed to provide coverage of routine operations, with internal audit activity targeted at the riskier or more complex.
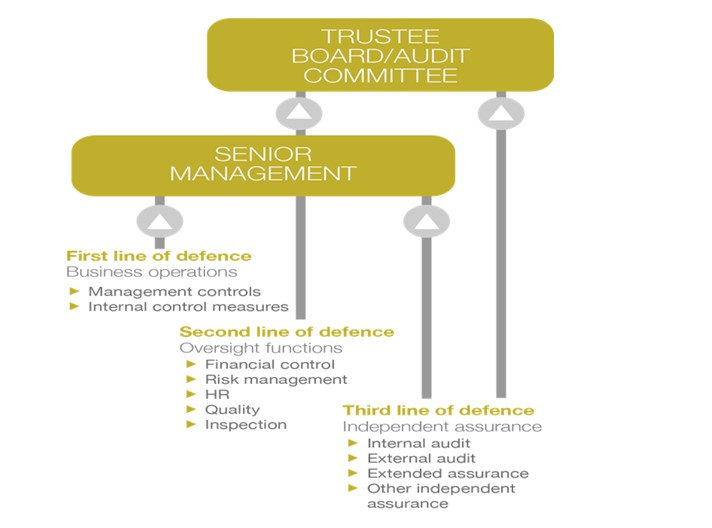
The Institute of Internal Auditors explains that in the Three Lines of Defence model, management control is the first line of defence in risk management, the various risk control and compliance oversight functions established by management are the second line of defence, and independent assurance is the third.
Each of these three ‘lines’ plays a distinct role within the organisation’s wider governance framework.
First line of defence
The first line of defence includes the ‘frontline’ or business operational areas. There are many arrangements established that can be used to derive assurance on how well objectives are being met and risks managed; for example, good policy and performance data, monitoring statistics, risk registers at country and central level, reports on the routine system controls and other management information.
The assurance at this level comes direct from those responsible for delivering specific objectives or operation; it provides assurance that performance is monitored, risks identified and addressed and objectives are being achieved.
While it may be that this type of assurance lacks independence and objectivity, its value lies in the fact that it comes from those who know the business, culture and day-to-day challenges.
Second line of defence
The second line of defence is associated with oversight of management activity. It is separate from those responsible for delivery, but not independent of the organisation’s management chain.
This could typically include compliance assessments or reviews carried out to determine that policy or quality arrangements are being met in line with expectations for specific areas of risk across the organisation.
This assurance provides valuable management insight into how well work is being carried out in line with set expectations and policy or regulatory considerations. It will be distinct from and more objective than first line assurance.
Third line of defence
The third line of defence relates to independent and more objective assurance and focuses on assurance to provide an independent and objective opinion on the framework of governance, risk management and control.
Internal audit places reliance upon assurance mechanisms in the first and second lines of defence, where possible, to enable it to direct its resources most effectively, on areas of highest risk or where there are gaps or weaknesses in other assurance arrangements.
It should also take assurance from other independent assurance providers operating in the third line, such as those provided by funder grant reviews, local external audits and work carried out as part of the external audit.
Serious incident reporting to the Charity Commission
Linked to the area of fraud and error is the Charity Commission’s regime on serious indecent reporting (SIR). We emphasise that (the SIR duty does not exist only in the case of fraud but in many other areas). The Charity Commission has updated its guidance on SIR.
This duty requires the Board to evaluate for themselves the level of risk to the charity or any vulnerable beneficiaries in respect of each SIR situation or ‘incident’ arising, and themselves to blow the whistle to the Commission if and when regulatory intervention would be likely to result.
There is often the issue of an unconfirmed incident which may arise from an allegation or suspicion and the Commission’s guidance states:
'You should still report this to us if you have received information that leads you to believe or suspect that a serious incident has happened and you have reasonable grounds for the suspicion. Trustees are responsible for taking appropriate action in response to a suspicion or allegation in order to protect their charity from harm, and we will expect to know what you have done. One of our statutory functions is to identify and investigate apparent misconduct or mismanagement in the administration of charities. We decide our regulatory response, if any, on the basis of evidence. If you are unsure whether an incident is serious or significant, we recommend you report it to us.'
This means that all frauds need to be recorded and charities should have a risk register and a risk log.
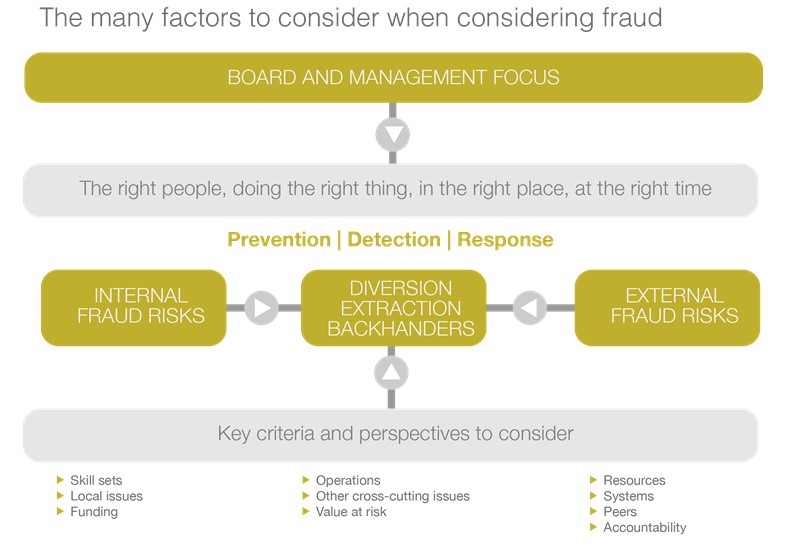
Prevention is always better than cure and ensuring the likelihood of detection is an important prevention tool.
Therefore, it is important that management and internal/ external auditors closely monitor and understand the business and investigate unusual variances. The culture should not permit management override and all staff should be aware of the risk of fraud and error.
A number of frauds are carried out by the ‘trusted’ individual and my experience of investigating these has made me a bit of a cynic. I now operate on the basis of ‘in God I trust — everyone else is subject to audit!’

Examples of well-known frauds at non-profits
The examples below highlight some frauds in the non-profit sector. It is apparent that the use of internal controls would prevent and/or detect similar frauds.
Bank account fraud
This organisation was in the midst of a major appeal. New donors were being solicited and there was very little trend analysis available.
One individual was responsible for both soliciting and receiving donations. In addition, she was also responsible for banking the donations. There were two bank accounts involved in the fraud: the main bank account of the organisation and another, now dormant, bank account that had been opened some years previously for a special fund-raising event. The auditors were not aware of the existence of the second bank account.
The fraudster originally started by ‘borrowing’ about £500 for a holiday. Apparently, the intention was to repay this, but of course, it never happened. The fraudster managed to use both frauds of diversion and of extraction defrauding the organisation by about £2.5 million.
In essence, the fraud was quite simple. A number of the cheques were banked into the second account which no one knew anything about and the fraudster withdrew these for her own use. Her spending became so large that she then had to make transfers from the main bank account of the charity to cover it. She did this in two ways.
In some cases, she transferred money directly from the first bank account to the second and in others she used the first bank account to make payments (through forged cheques) purportedly on behalf of the charity which were for her own extravagant lifestyle.
To allay the suspicions of her colleagues, she explained her ‘inheritance’ and even made substantial donations to the charity. Surprisingly, she had been told by her superiors to close the second account and they were seemingly unaware that this had not been done.
The amount stolen was a significant percentage of the charity’s income. However, since the charity was in the stage of early donor development, those involved with managing the charity internally and in auditing it, did not notice that large amounts were being diverted. The whole system was flawed because there were no internal controls and it was based entirely on trust.
The main problem was the lack of segregation of duties on areas that should have been separated, such as soliciting the income, receiving and opening the mail, recording the income and banking.
This was not a large charity and therefore full segregation of duties would not have been possible. However, it would have been important for the charity to have some compensating controls, segregating the main duties. In addition, there should have been some form of back-up checking through independent means with the donors.
Security of cheques fraud
This large national charity was in a period where the amount of cheques received was greater than it could process in a timely manner. Consequently, these cheques were being ‘locked away’ by the cashier.
The charity was commonly known by its initials and donors wrote cheques using those initials. The cashier was able to open a bank account in a name that, with a little amendment, incorporated the charity’s initials. As a result, he was able to divert over £800,000.
Many charities prevent subsequent diversion of their cheques by the use of a simple stamp across their cheques which states the charity’s bank account number and its bank sort code, thus the cheques cannot be banked in any other bank account. This also highlights the importance of prompt recording and banking of donations.
Controls over post opening are important and these should exist at all the locations where cash and cheques are received.
Branch fraud
This international NGO operated through a number of fundraising branches during a major international disaster. The branches were encouraged to carry out local fundraising events and were supported by head office in their endeavours to do so.
In the end, the branches were required to fill in a branch return to analyse their income and expenditure and, supposedly, tie in to the amounts being sent to head office.
The branch treasurer, knowing that the branch committee would be aware of the amounts raised by the branch, produced a set of figures for them which did not, in fact, tie in with the branch return or the amounts she was remitting to head office. This fraud involved almost £20,000 and controls now in place would detect a similar occurrence.
The organisation now has a regional manager who is closely involved with the activities of the branches and is aware of the amounts that should appear on the branch return. The branch return itself is required to be presented to the full branch committee who should notice any anomalies between the amounts that they would expect to see on it and the amounts that were included on it.
The organisation is also closely matching amounts received by branches and amounts stated as being received on their branch return. (Surprisingly, a number of non-profits do not attempt to reconcile differences of transactions between the head office and the branch and they are naïvely treated as, ‘Okay to write-off as it is all in the family’!)
BACS fraud
This organisation used a manual BACS form for its payments. The form involved the name of the payee, the special BACS number and the amount. The form was prepared by the finance officer and usually signed off by another individual, such as the chief executive.
The finance officer used a number of ploys to extract over £100,000 from the organisation. In some instances, he used fictitious invoices for budgeted expenditure, such as repairs, and simply inserted his own BACS transfer number against the payee details.
Of course, the signatory was not checking that the numbers matched the payees. In other cases, the finance officer did not have to prepare fictitious invoices as he simply added on another name to the bottom of the form and was able to amend the total that had been authorised by the signatory.
Once again, a lack of segregation of duties and no independent checks of expenditure incurred allowed this fraud to occur.
Legacies fraud
The legacy officer of this organisation wrote to the executors asking them to pay legacies directly into a bank account that had been opened by him and was not within the accounting records and controls of the organisation. The executors were not aware of any problem and simply made the payments accepting ‘receipt’ from the legacy officer.
The opening of unauthorised bank accounts has become much harder as a result of an initiative between the Charity Finance Group, the Charity Commission and the British Bankers’ Authority. Most banks will now refuse to open an account in the name of the charity unless they have the appropriate authority from the head office.
Notwithstanding, this system can be circumvented and charities should not rely on this control. They should have their own internal controls to prevent cheques from being misappropriated.
Payments fraud
This fraud involved collusion between a supplier and a charity employee. The supplier billed the charity employee for work that was never carried out. This work involved services that could not easily be verified. The supplier was regularly billing the charity for de-duping mailing lists, sorting its mailing list, profiling donors, etc. The charity employee authorised the invoices and received a share.
In some cases, purchasing fraud is less blatant. Charity employees receive kickbacks, gifts and other incentives to use a particular supplier when the use of that supplier and its products is not in the best interest of the charity. Standard controls over the purchase, creditors and payments cycle should help such frauds, but it is very difficult to cater for collusion.
Grants fraud
A charity applied for and received a grant for £50,000. This had been a head office initiative for a local project. The project manager subsequently approached the funder for a ‘top up’ grant of £10,000 that was received at the project and never used for the charity.
The head office’s records and budget tied in with the project’s figures and agreed with the original budget application. It was only direct confirmation sought by the auditors that identified that an additional £10,000 had been paid.
Shops fraud
The shop’s manager ‘tilled up’ an hour before the shop closed each evening. During this period, she worked alone and pocketed the takings. The earlier till readings matched taking records and cash banked.
The fraud was discovered by random test purchase checks. Further investigation revealed that the fraudster was also stealing donated goods and selling them on a second hand goods market. Once again, segregation of duties and proper tilling and checking procedures should have prevented this fraud.
Journal fraud
An employee in the finance department of the charity obtained cheques that were due to the charity and diverted them. He was aware that the income section were expecting the income so he used journals to record the income by way of credit entry but the debit entry was to different ledger accounts and not to the bank account.
The debit entries were often queried by account holders and he simply responded that it was a posting error and journaled them to another account. Controls over cheques and controls over journals were weak and this combination allowed the fraudster to steal over £90,000.
Diversion of income
The programme director of an overseas project was diverting sums of money that were being generated locally. This included the setting up of an ‘internet café’ on the charity’s premises and local fundraised income. A separate bank account that was never on the books had been opened.
Internal controls
Good practice suggests consideration of the following types of internal control.
Organisational: The organisation should have a plan of its organisation, defining and allocating responsibilities and identifying lines of reporting for all aspects of its operations, including the controls. The delegation of authority and responsibility should be clearly specified.
Segregation of duties: One of the prime means of control is the separation of those responsibilities or duties which would, if combined, enable one individual to record and process a complete transaction. Segregation of duties reduces the risk of internal manipulation or error and increases the element of checking.
Functions which should be separated include those of soliciting income, receiving and opening mail, recording income, banking, authorisation, execution and custody. Full segregation of duties may not be possible in all cases and this will require the use of other compensating control procedures.
Physical: These are concerned mainly with the custody of assets and involve procedures and security measures designed to ensure that access to assets is limited to authorised personnel. This includes both direct access and indirect access via documentation. These controls assume importance in the case of valuable, portable, exchangeable or desirable assets.
Authorisation and approval: All transactions should require authorisation or approval by an appropriate responsible person. The limits for these authorisations should be specified by the trustees/management.
Arithmetical and accounting: These are the controls within the recording function which check that the transactions to be recorded and processed have been authorised, that they are included and that they are correctly recorded and accurately processed. Such controls include checking the arithmetical accuracy of the records, the maintenance and checking of totals, reconciliations, control accounts and trial balances and accounting for documents.
Personnel: There should be procedures to ensure that personnel have capabilities commensurate with their responsibilities. Inevitably, the proper functioning of any system depends on the competence and integrity of those operating it. The qualifications, selection and training as well as the innate personal characteristics of the personnel involved are important features to be considered in setting up any control system.
Supervision: Any system of internal control should include the supervision by responsible officials of day to pay transactions and recording.
Management: These are the controls exercised by the Board and management outside the day to day routine of the system. They include the overall supervisory controls exercised by Boards/management, the review of management accounts and comparison thereof with budgets, the internal audit function and any other special review procedures.